| Skip Navigation Links | |
| Exit Print View | |

|
Oracle Solaris 11.1 Administration: Security Services Oracle Solaris 11.1 Information Library |
| Skip Navigation Links | |
| Exit Print View | |

|
Oracle Solaris 11.1 Administration: Security Services Oracle Solaris 11.1 Information Library |
1. Security Services (Overview)
Part II System, File, and Device Security
2. Managing Machine Security (Overview)
3. Controlling Access to Systems (Tasks)
4. Virus Scanning Service (Tasks)
5. Controlling Access to Devices (Tasks)
6. Verifying File Integrity by Using BART (Tasks)
7. Controlling Access to Files (Tasks)
Part III Roles, Rights Profiles, and Privileges
8. Using Roles and Privileges (Overview)
9. Using Role-Based Access Control (Tasks)
10. Security Attributes in Oracle Solaris (Reference)
Part IV Cryptographic Services
11. Cryptographic Framework (Overview)
12. Cryptographic Framework (Tasks)
Part V Authentication Services and Secure Communication
14. Using Pluggable Authentication Modules
17. Using Simple Authentication and Security Layer
18. Network Services Authentication (Tasks)
19. Introduction to the Kerberos Service
20. Planning for the Kerberos Service
21. Configuring the Kerberos Service (Tasks)
22. Kerberos Error Messages and Troubleshooting
23. Administering Kerberos Principals and Policies (Tasks)
24. Using Kerberos Applications (Tasks)
25. The Kerberos Service (Reference)
Part VII Auditing in Oracle Solaris
Audit Terminology and Concepts
Audit Classes and Preselection
Audit Records and Audit Tokens
Storing and Managing the Audit Trail
How Is Auditing Related to Security?
Auditing on a System With Oracle Solaris Zones
During system configuration, you preselect which classes of audit records to monitor. You can also fine-tune the degree of auditing that is done for individual users. The following figure shows details of the flow of auditing in Oracle Solaris.
Figure 26-1 The Flow of Auditing
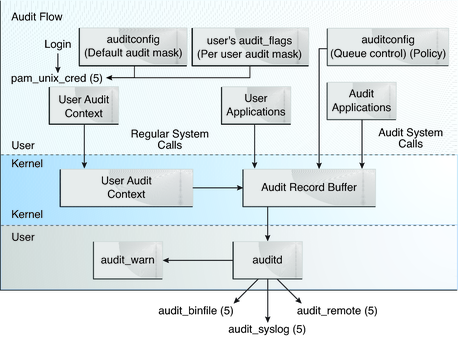
After audit data is collected in the kernel, plugins distribute the data to the appropriate locations.
The audit_binfile plugin places binary audit records in the /var/audit file system. By default, the audit_binfile plugin is active. Post-selection tools enable you to examine interesting parts of the audit trail.
Audit files can be stored in one or more ZFS pools. These pools can be on different systems and on different but linked networks. The collection of audit files that are linked together is considered an audit trail.
The audit_remote plugin sends binary audit records across a protected link to a remote repository.
The audit_syslog plugin sends text summaries of audit records to the syslog utility.
Systems that install non-global zones can audit all zones identically from the global zone. These systems can also be configured to collect different records in the non-global zones. For more information, see Auditing and Oracle Solaris Zones.